Regulating Cybersecurity for Electric Power Systems: Preliminary Findings from CIGRE WG D2.54
 |
 |
 |
|||
|
Ugo Finardi WG Co-Convenor |
Elena Maria Ragazzi WG Co-Convenor |
Victor Tan SC D2 Chair |
As cyber threats to critical infrastructure grow in both scale and sophistication, the question of how to effectively regulate cybersecurity for electric power systems has become a pressing concern worldwide. Which regulatory approaches deliver real improvements in security posture? How should investment in cyber protection be measured and incentivised? And who ultimately bears the cost?
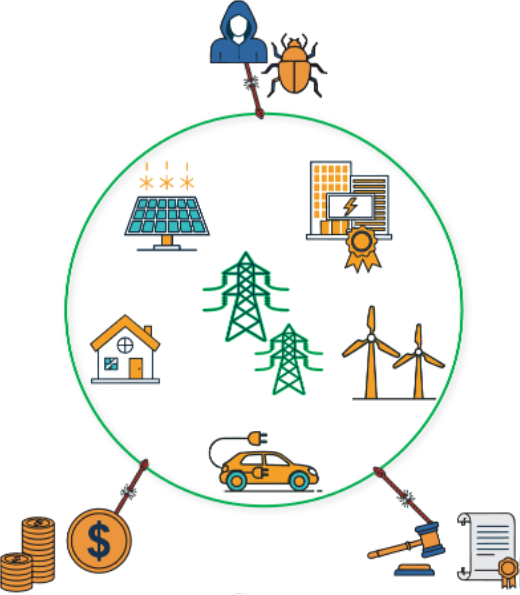
Figure 1 - Today's interconnected grid is pulled by competing forces: cyber threats, regulatory effectiveness, and the economics of protection.
CIGRE Working Group D2.54 was established to examine these questions, bringing together twenty-four experts from sixteen countries. Its forthcoming Technical Brochure analyses the regulatory landscape and offers evidence-based frameworks for strengthening cybersecurity governance in the electricity sector.
The WG first developed a theoretical foundation for understanding the specific economic challenges of cybersecurity regulation. A central insight is that cybersecurity in interconnected power systems often functions as a public good — its benefits extend to all grid participants, not only to those who invest in protection. When one utility strengthens its defences, neighbouring systems also become more secure, even without having contributed to the cost. This creates a fundamental challenge for regulators: how can investment incentives be structured when the returns on cybersecurity spending are shared broadly? Addressing this question requires reliable management metrics to assess both the effectiveness and cost-effectiveness of protection measures.
The theoretical framework also examines two further dimensions critical to regulatory design: the growing risks posed by supply chain attacks, where vulnerabilities in a single vendor’s products can cascade across multiple utilities; and the essential role of information sharing between organisations in building collective resilience against emerging threats.
To understand current regulatory practice, the WG conducted two international surveys: one directed at regulated electricity utilities and the other at regulatory agencies. The responses reveal the significant complexity of managing cybersecurity within electric power systems. While most countries have enacted general cybersecurity legislation, regulations specifically tailored to the electricity sector remain uncommon. Both utilities and regulators identified a pressing need for better alignment between cyber and physical security frameworks. A persistent theme was the economics of cybersecurity: many regulators do not systematically monitor what utilities spend on cyber protection, and utilities themselves often struggle with cost tracking and recovery. Encouragingly, however, both groups demonstrated notable proactivity — there is broad recognition across the sector that keeping pace with an evolving threat landscape is essential.
Building on the available survey data, the WG developed and experimented a maturity scoring methodology aimed at assessing how advanced a utility’s cybersecurity posture is relative to its peers. By assigning quantitative scores to selected responses and aggregating them into a composite indicator, the approach creates a measurable baseline for cross-jurisdictional comparison. While the methodology requires further refinement, by designing a more targeted questionnaire, it demonstrates a practical path toward comparable cybersecurity metrics that could be applied by CIGRE working groups and inform the comparison among very different operational systems and regulatory frameworks.
The Technical Brochure also presents eight national case studies spanning all continents, examining how countries have addressed cybersecurity regulation in practice. These reveal substantial differences in power grid structures, governance arrangements, and levels of policy maturity, shaped by the historical, political, and geographical context of each country. The degree of grid integration varies significantly — from highly centralised systems to extensively distributed architectures — directly affecting the scale of the cyber attack surface. Despite this diversity, the importance of cybersecurity is universally acknowledged. The case studies also illuminate differing approaches to funding: some countries have established regulatory mechanisms that pass cybersecurity costs through to consumers, while others rely on government programmes to finance training and protective measures.
WG D2.54’s work delivers a clear message to decision-makers: effective cybersecurity regulation for electric power systems must recognise the public-good nature of cyber protection, establish consistent frameworks for measuring maturity, and be flexible enough to accommodate the diversity of national grid architectures. As cyber threats continue to evolve, the Working Group’s findings provide a timely evidence base for regulators and utilities worldwide who are working to strengthen their approach to this critical challenge.
